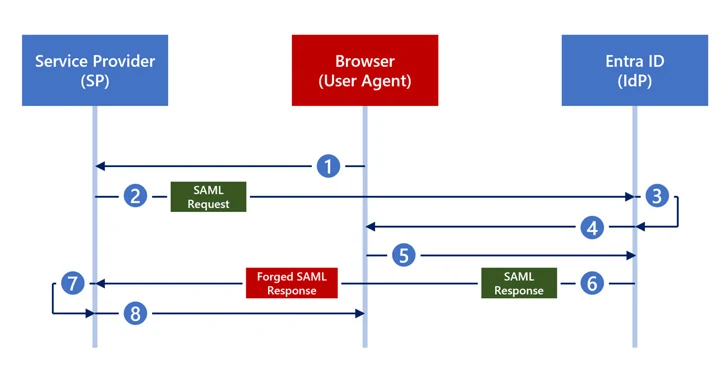
New Silver SAML Attack Evades Golden SAML Defenses in Identity Systems
[ad_1] Feb 29, 2024NewsroomThreat Intelligence / Cyber Threat Cybersecurity researchers have disclosed a new attack technique called Silver SAML that can be successful even in cases where mitigations have been applied against Golden SAML attacks. Silver SAML “enables the exploitation of SAML to launch attacks from an identity provider like Entra ID against applications configured…