Iranian MuddyWater Hackers Adopt New C2 Tool ‘DarkBeatC2’ in Latest Campaign
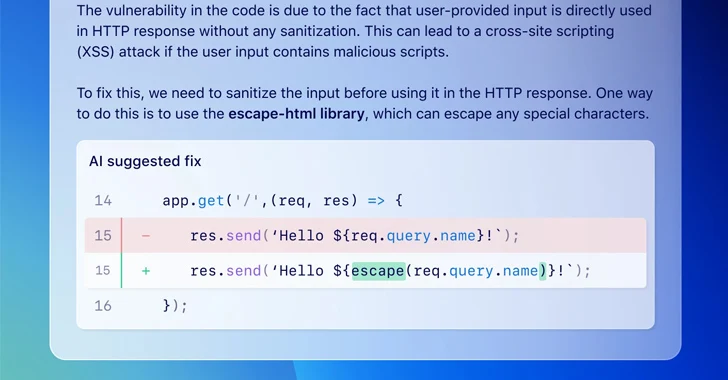
[ad_1] The Iranian threat actor known as MuddyWater has been attributed to a new command-and-control (C2) infrastructure called DarkBeatC2, becoming the latest such tool in its arsenal after SimpleHarm, MuddyC3, PhonyC2, and MuddyC2Go. “While occasionally switching to a new remote administration tool or changing their C2 framework, MuddyWater’s methods remain constant,” Deep Instinct security researcher…