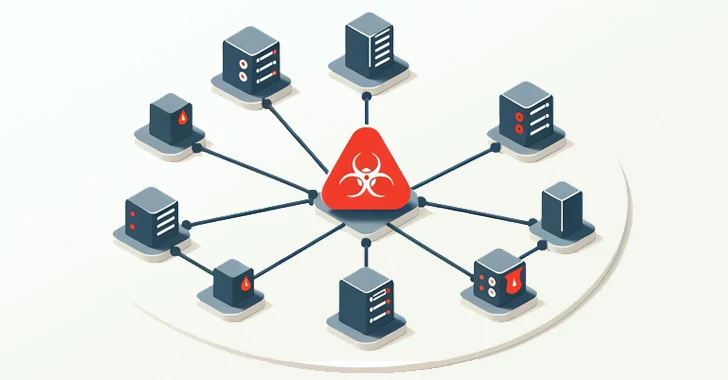
HeadCrab 2.0 Goes Fileless, Targeting Redis Servers for Crypto Mining
[ad_1] Feb 01, 2024NewsroomCryptocurrency / Botnet Cybersecurity researchers have detailed an updated version of the malware HeadCrab that’s known to target Redis database servers across the world since early September 2021. The development, which comes exactly a year after the malware was first publicly disclosed by Aqua, is a sign that the financially-motivated threat actor…