New BIFROSE Linux Malware Variant Using Deceptive VMware Domain for Evasion
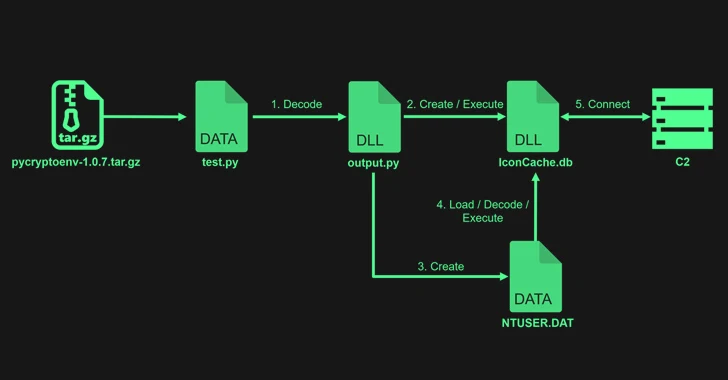
[ad_1] Mar 01, 2024NewsroomLinux / Cyber Threat Cybersecurity researchers have discovered a new Linux variant of a remote access trojan (RAT) called BIFROSE (aka Bifrost) that uses a deceptive domain mimicking VMware. “This latest version of Bifrost aims to bypass security measures and compromise targeted systems,” Palo Alto Networks Unit 42 researchers Anmol Maurya and…