[ad_1]
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Thursday added a now-patched security flaw impacting Cisco Adaptive Security Appliance (ASA) and Firepower Threat Defense (FTD) software to its Known Exploited Vulnerabilities (KEV) catalog, following reports that it’s being likely exploited in Akira ransomware attacks.
The vulnerability in question is CVE-2020-3259 (CVSS score: 7.5), a high-severity information disclosure issue that could allow an attacker to retrieve memory contents on an affected device. It was patched by Cisco as part of updates released in May 2020.
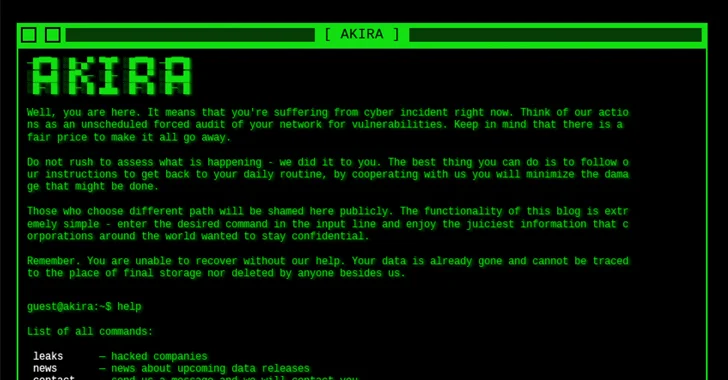
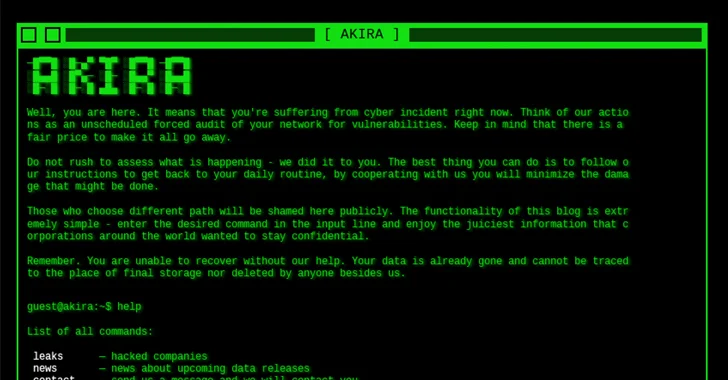
Late last month, cybersecurity firm Truesec said it found evidence suggesting that it has been weaponized by Akira ransomware actors to compromise multiple susceptible Cisco Anyconnect SSL VPN appliances over the past year.
“There is no publicly available exploit code for […] CVE-2020-3259, meaning that a threat actor, such as Akira, exploiting that vulnerability would need to buy or produce exploit code themselves, which requires deep insights into the vulnerability,” security researcher Heresh Zaremand said.
According to Palo Alto Networks Unit 42, Akira is one of the 25 groups with newly established data leak sites in 2023, with the ransomware group publicly claiming nearly 200 victims. First observed in March 2023, the group is believed to share connections with the notorious Conti syndicate based on the fact that it has sent the ransom proceeds to Conti-affiliated wallet addresses.
In the fourth quarter of 2023 alone, the e-crime group listed 49 victims on its data leak portal, putting it behind LockBit (275), Play (110), ALPHV/BlackCat (102), NoEscape (76), 8Base (75), and Black Basta (72).
Federal Civilian Executive Branch (FCEB) agencies are required to remediate identified vulnerabilities by March 7, 2024, to secure their networks against potential threats.
CVE-2020-3259 is far from the only flaw to be exploited for delivering ransomware. Earlier this month, Arctic Wolf Labs revealed the abuse of CVE-2023-22527 – a recently uncovered shortcoming in Atlassian Confluence Data Center and Confluence Server – to deploy C3RB3R ransomware, as well as cryptocurrency miners and remote access trojans.
The development comes as the U.S. State Department announced rewards of up to $10 million for information that could lead to the identification or location of BlackCat ransomware gang key members, in addition to offering up to $5 million for information leading to the arrest or conviction of its affiliates.
The ransomware-as-a-service (RaaS) scheme, much like Hive, compromised over 1,000 victims globally, netting at least $300 million in illicit profits since its emergence in late 2021. It was disrupted in December 2023 following an international coordinated operation.
The ransomware landscape has become a lucrative market, attracting the attention of cybercriminals looking for quick financial gain, leading to the rise of new players such as Alpha (not to be confused with ALPHV) and Wing.
The U.S. Government Accountability Office (GAO), in a report published towards the end of January 2024, called for enhanced oversight into recommended practices for addressing ransomware, specifically for organizations from critical manufacturing, energy, healthcare and public health, and transportation systems sectors.
[ad_2]
Source link